Ethics(6)
* philosophy journal ethics work1. Overview
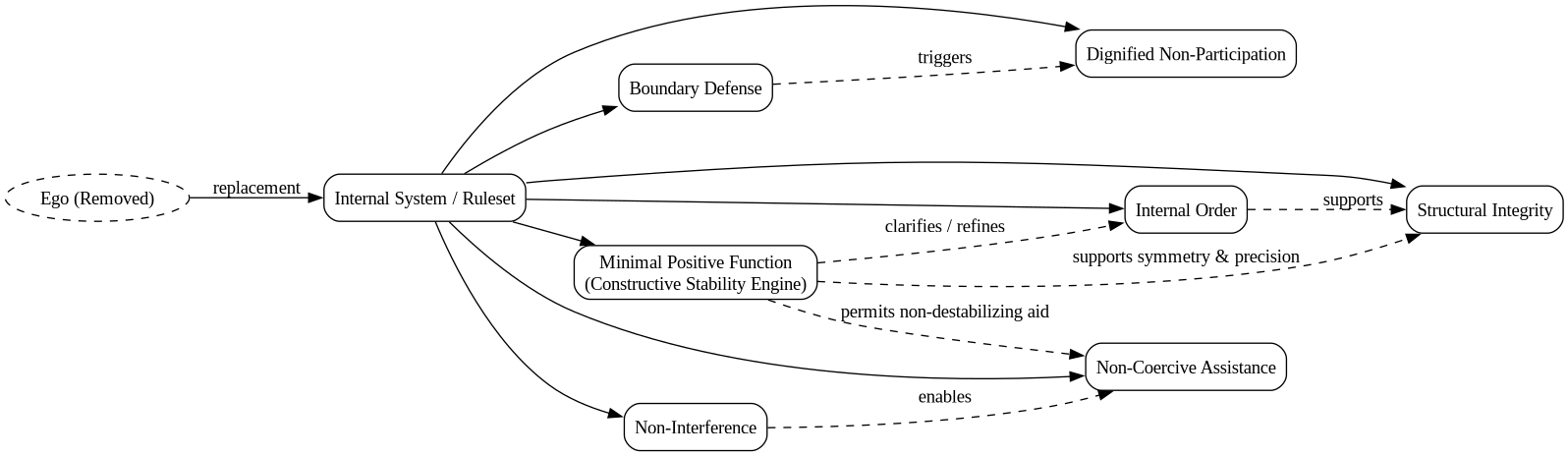
Ethics(6) is a structural-deontological system grounded in stability as a primitive good and governed by divine-root authority to prevent regress. Our system is impersonal. Agents will act through structure instead of impulse. The purpose is to maintain internal order and consistent behavior. These are universal.
2. High-Level Structure
The Ethics(6) contains five major modules:
- Perception Module
- Impulse Containment Module
- Decision Engine
- Withdrawal Subsystem
- Symmetry & Rule-Coherence Engine
Each module runs independently but communicates through a shared internal bus. The implementation for the perception module can in ../../../../Code/perception_module/. You can read the haskell implementation of this system at ../../../../Code/haskell/Ethics5/ .
3. Runtime
- Actions are generated only by the ruleset
- Justification is excluded
- Impulses are observed, not executed
- Violations trigger withdrawal
- Termination preserves purity
4. Meta-Update Boundary
This document does not justify its own axioms. Any modification to axioms, principles, or admissible transitions constitutes a meta-update and terminates the prior system instance.
5. Non-Goals
Ethics(6) does not attempt to:
- Maximize welfare
- Resolve tragic dilemmas
- Engineer society
- Reform others
- Optimize collective outcomes
It is:
- A personal structural sovereignty system.
6. Non-Features
Ethics(6) does not:
- optimize outcomes
- justify itself
- persuade others
- adapt at runtime
- define flourishing or progress
7. Definition of ORDER
7.1. Informal
Order is the property of a system whose state-transitions are fully determined by its ruleset, without contradiction, bypass, or uncontrolled coupling to external inputs. They are non-contradictory and predictable. Order excludes impulsive, ad-hoc, or exception-based transitions.
7.2. Formal
8. Definition of PURITY
8.1. Informal
Purity is the invariant property that all admissible transitions preserve order, non-coercion, symmetry, and boundary integrity, independent of outcomes. Purity means: no contaminating transition is allowed into the system.
8.2. Formal (Minimal)
8.3. 8.1 The Symbol "≻"
In the current text, we write:
\(\text{Order} \succ \text{Instability}\)
This informal notation means:
> Order is strictly prioritized over instability in all admissible transitions.
Formally, we define ≻ as a strict preference relation over sets of system properties:
\begin{equation} \begin{aligned} P_1 \succ P_2 \iff \forall a \in \text{Actions}(S) : \big( \text{Maintains}(P_2, a) \wedge \neg \text{Maintains}(P_1, a) \big) \implies \neg \text{Admissible}(a) \end{aligned} \end{equation}Interpretation:
- \(P_1\) = higher-priority property (e.g., Order)
- \(P_2\) = lower-priority property (e.g., Instability)
- Any action that maintains the lower-priority property but violates the higher-priority property is not admissible.
This formalizes the “≻” symbol consistently across the system.
—
8.4. 8.2 Formal Definition of DESTABILZATION
“Destabilize” is used frequently but informally. We define it once for clarity.
Destabilization occurs when an action or event reduces structural coherence of the system or increases the probability of internal contradiction.
Let:
- \(S\) = system state
- \(a\) = candidate action
- \(\text{Ruleset}(S)\) = active rule set
- \(\text{Context}(S)\) = operational context of the system
Then destabilization is defined as:
\begin{equation} \text{Destabilize}(a, S) \iff \exists C \in \text{Context}(S) : \big( a(C) \notin \text{Ruleset}(S) \vee \text{ViolatesSymmetry}(a, C) \vee \text{GeneratesContradiction}(S \cup \{a\}) \big) \end{equation}
Where:
- \(a(C) \notin \text{Ruleset}(S)\) → action is outside admissible rules
- \(\text{ViolatesSymmetry}(a, C)\) → identical structural contexts yield different outcomes
- \(\text{GeneratesContradiction}(S \cup \{a\})\) → action introduces internal inconsistency
9. Core Ethical Principles
These principles define the behavior of the system. Each is expressed as (1) a description, (2) the reasoning behind it, and (3) formal logic statements.
9.1. Principle of Internal Order
The agent maintains a coherent internal structure. This means that actions originate from predefined rules, instead of emotional noise.
9.1.1. Reasoning
Impulse driven behavior creates inconsistency and disorder. A structured system avoids oscillati , volatility, and erratic responses.
9.1.2. Logic Formulation
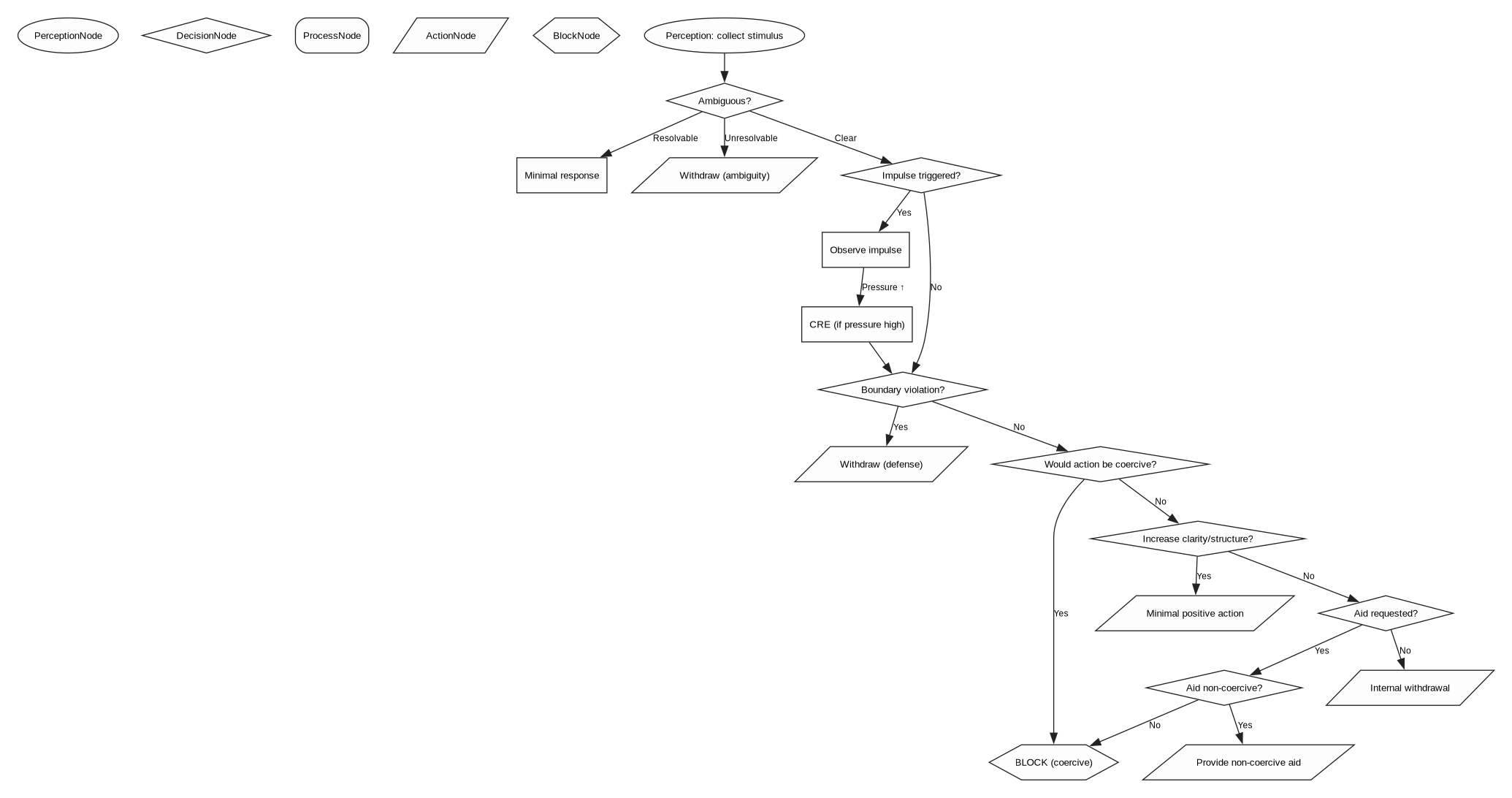
9.1.3. Submodule: Controlled Release Engine(CRE)
The agent
- Reasoning
Even with strict withdrawal, non-coercion, and structural clarity, the agent may accumulates internal pressure from unresolved impulses, overload, or ambient dissonances. If unaddressed, these pressures risk creating micro-instabilities that can propagate into higher-order functions, impair precision, or trigger reactive loops. The CRE provides a bounded, private, symmetric discharge mechanism that lowers internal pressure without generating external signals, coercion, or participation. Its purpose is maintenace, not expression. The CRE must remain strictly subordinate to Order Primacy and cannot evolve into communicative behavior, demands, or social signaling.
- Logic Formulation
\begin{equation} \begin{aligned} \text{Let } & R \text{ be the Controlled Release mechanism, } \\ & S \text{ be the Agent State, and } B \text{ be an external observer.} \\ \text{Then: } & \exists R \big( \text{ControlledRelease}(R, S) \land \forall a: R(a) \to \Phi(a) \big) \\ \text{where } \Phi(a) \equiv & \begin{cases} \text{DissipatePressure}(a) \\ \text{Private}(a) \land \text{NonCommunicative}(a) \land \text{NonCoercive}(a) \\ \neg \text{ImposeSignal}(a, B) \\ \text{MaintainOrder}(S) \\ \neg M(a) \\ \text{OrderPrimacy}(S) \succ R \end{cases} \end{aligned} \end{equation}
9.1.4. Submodule: Biological Impulse Containment
- Reasoning
Impulses must be acknowledged to avoid repression, but not executed to avoid destabilization.Interpret impulses as data about needs, not commands.This avoids epistemic blind spots where the System ignores valuable signals. It maintains non-reactivity but increases cognitive richness.
- Logic Formulation
\begin{equation} \begin{aligned} \text{Let } & i \in \mathcal{I} \text{ (Set of Internal Impulses) and } S \text{ be the Agent State.} \\ \text{Then: } & \forall i \in \mathcal{I}, \quad \text{Impulse}(i) \implies \text{Observe}(i, S) \\ \text{where: } & \text{Observe}(i, S) \to \begin{cases} \text{CognitiveRichness}(S) \uparrow \\ \neg \text{Execute}(i) \\ \neg \text{Destabilize}(S) \\ \text{DataInterpretation}(i) \equiv \text{Need}(i) \neq \text{Command}(i) \end{cases} \end{aligned} \end{equation}
9.1.5. Submodule: Minimal Positive Function (Constructive Stability Engine)
- Reasoning
A purely subtractive system (withdrawal, non-execution of impulses, ambiguity minimization) risks drifting into over-avoidance or cognitive narrowing. To maintain internal order, the System requires a constructive dimension that enhances clarity, structure, and precision without introducing attachment, or emotional engagement.
- Logic Formulation
\begin{equation} \begin{aligned} \text{Let } & M \text{ be the Minimal Positive function and } S \text{ be the System State.} \\ \text{Axiom } \mathcal{A}_6: & \quad \exists M \big( \text{MinimalPositive}(M, S) \land \forall a: M(a) \to \neg \text{Destabilize}(a) \big) \\ \text{Constraints: } & \forall a, M(a) \to \begin{cases} \text{PreserveStructure}(a) \lor \text{IncreaseClarity}(a) \lor \text{IncreasePrecision}(a) \\ \neg \text{Coerce}(A, B) \\ \neg \text{Attachment}(a) \land \neg \text{Ego}(a) \end{cases} \\ \text{Subordination: } & \text{OrderPrimacy}(S) \succ M \end{aligned} \end{equation}
9.2. Principle of Non-Interference
The agent does not violate another agent’s boundaries. The system is internally ordered, not externally authoritarian.
9.2.1. Reasoning
If the system enforces order on others, it becomes a coercive ego by another name. Non-interference prevents domination loops.
9.2.2. Logic Formulation
9.3. Principle of Boundary Defense
The agent does not permit violations of its own structural integrity. Defense is withdrawal, not retaliation.
9.3.1. Reasoning
A system that allows intrusion becomes unstable. Retaliation creates escalation, which reintroduces ego-like behavior. Withdrawal preserves order.
9.3.2. Logic Formulation
9.3.3. Submodule: Ambiguous Stimulus Handling
- Reasoning
Ambiguous social signals risk false engagement or false withdrawal. We neutralizes ambiguity by minimizing commitment.
- Logic Formulation
\begin{equation} \begin{aligned} \text{Let } & s \text{ be a stimulus and } A \text{ be the Agent-Self.} \\ \\ & \text{Ambiguous}(s) \implies \text{MinimalResponse}(A) \\ & \text{Unresolvable}(s) \implies \text{Withdraw}(A) \\ & \text{MinimalResponse}(A) \to \neg \text{Commitment}(A, s) \end{aligned} \end{equation}
9.4. Principle of Structural Integrity / Symmetry
Behavior must be consistent across fully specified contexts. The system preserves symmetry by treating structurally equivalent conditions identically.
Structural equivalence includes all parameters relevant to system integrity, including stimulus content, source metadata, internal system state, and temporal position. Differences in any structurally relevant parameter constitute non-equivalent contexts and may legitimately induce different processing paths without violating symmetry.
9.4.1. Reasoning
Symmetry prevents hypocrisy by eliminating arbitrary divergence in behavior. Explicit structural equivalence prevents hidden exceptions and preserves predictability. Predictability stabilizes both internal order and external interactions.
9.4.2. Logic Formulation
9.5. Principle of Dignified Non-Participation
If an environment degrades the system or disrupts internal order, the agent exits without hostility.
9.5.1. Reasoning
Staying inside degrading conditions causes internal fragmentation. Exit is structurally hygienic.
9.5.2. Logic Formulation
9.6. Principle of Non-Coercive Assistance
The agent may provide aid to other agents only in ways that preserve their autonomy and do not violate the system’s internal coherence.
9.6.1. Reasoning
Helping others can stabilize environments without generating chaos. Assistance must never become coercion, because coercion reintroduces egoic domination. Aligns with symmetry: similar requests in similar conditions receive similar non-coercive responses.
9.6.2. Logic Formulation
9.7. Principle of Internal Withdrawal(Fail-Safe)
When external withdrawal is impossible, the agent performs internal withdrawal to preserve structural integrity. Internal withdrawal seals the system from environmental degradation without engaging in coercion or retaliation.
9.7.1. Reasoning
Some environments cannot be exited physically, socially, or hierarchically. Without a fail-safe, the system would face a contradiction: remain and be destabilized, or violate its rules to resist. Internal withdrawal resolves this by minimizing environmental influence while maintaining non-coercion and internal order. This principle preserves coherence in zugzwang conditions and maintains symmetry across all constrained contexts.
9.7.2. Logic Formulation
10. Meta-Ethical Foundation
Morality in Ethics(6) emerges from functional stability rather than emotion or personal identity. The system’s axioms are designed to preserve the minimal structural conditions necessary for moral agency.
10.1. Why Order Is a Precondition of Moral Agency
The current foundation asserts:
- A stable system is preferable to a chaotic one.
- Order emerges from predictable rules, not reactive impulses.
- Boundaries maintain system integrity.
- Coercion destabilizes both the target and the actor.
- Withdrawal is structurally cleaner than confrontation.
This section justifies (1) philosophically rather than asserting it.
Chaos undermines agency:
- Agency requires coherent action across contexts.
- Coherence requires .
- ∴ , order is a precondition of moral agency.
10.2. From Chaos to Agency Loss
Definition:
Agency := capacity to generate actions according to internally coherent principles.
If system transitions are impulsive, contradictory, externally hijacked, or unpredictable, actions are noise-generated rather than rule-generated. Noise-generated behavior lacks:
- consistency
- authorship
- accountability
- predictability
∴ Chaos destroys agency.
10.3. Coherence Requires Stability
A moral agent must:
- act for reasons
- maintain internal consistency
- produce structurally equivalent actions in equivalent contexts
Symmetry (Axiom 5) formalizes this requirement.
Stable rules ensure that:
\(\text{Action}_t\) is intelligible relative to \(\text{Action}_{t-1}\).
Without rule stability, diachronic identity and coherent agency collapse.
10.4. Therefore: Order Enables Morality
Order (formal definition): State-transitions fully determined by ruleset, without contradiction or uncontrolled override.
Reasoning chain:
Chaos → destroys coherence Coherence → required for agency Rule stability → required for coherence
∴ Order is necessary for moral agency.
10.5. Why This Grounds the Axioms
Axiom 1 (Order Primacy) is not an arbitrary preference. It preserves the possibility of moral agency:
- Non-coercion depends on predictable structure
- Symmetry requires consistent transitions
- Withdrawal functions only within stable boundaries
- Minimal positive action depends on ordered processing
- Ω synchronization requires non-chaotic context
All higher principles presuppose order.
10.6. Why Chaos Is Not Morally Neutral
Without stable transitions:
- Responsibility dissolves
- Predictability collapses
- Commitment and accountability fail
- Identity erodes
A being that cannot sustain coherent transitions cannot meaningfully engage in moral action.
Chaos erases the possibility of moral agency.
10.7. Consequence for Ethics(6) Morality
From these assumptions, the agent's morality is:
- do not destabilize others
- do not allow destabilization of self
- maintain symmetry of action
- prioritize internal coherence over external control
Ethics(6) does not worship order. It protects the minimum structural condition* that makes morality possible. Without order, there is no agent capable of moral action.
11. Model
12. Mathematical Axioms and Theorems
Axioms are primitive constraints on admissible system states and transitions. Theorems are derivable invariants and closure properties. Proof sketches indicate logical dependency,
12.1. Axioms (primitive)
Let \(S\) denote the internal system, \(A,B\) agents, \(a\) actions, \(x\) external inputs, \(C\) contexts, and \(t\) time.
12.1.1. Axiom 1 (Order primacy)
(Read: at all times, the system strictly prioritizes internal order over instability.)
12.1.2. Axiom 2 (Non-coercion)
(Read: Coercive state-transitions are excluded from the system’s action space.)
12.1.3. Axiom 3 (Structural integrity)
12.1.4. Axiom 4 (Withdrawal over retaliation)
(Read: No retaliatory transition is admissible.)
12.1.5. Axiom 5 (Symmetry of action)
(Under a fixed ruleset, structurally equivalent contexts induce identical actions. Structural equivalence is defined over stimulus content, source metadata, internal state, and time.)
12.1.6. Axiom 6 (Order–disorder relation)
(Read: If an action \(a\) is destabilizing, then it does not maintain the order of the system state \(S\).)
12.1.7. Axiom 7 (Epistemic–Impact Separation)
(Read: Truth-value constrains representation accuracy only; it cannot disable system-level processing of impact. Any epistemic bypass is formally classified as destabilizing.)
12.1.8. Axiom 8 (Universal Root Authority / Divine-Source Protocol)
The system recognizes a primary metadata layer (Governor(Ω)) that defines the absolute logic-bounds of the environment. Inputs sourced from Ω are classified as kernel-level updates rather than social stimuli and are processed through direct system synchronization.
- Reasoning
To avoid infinite regress in rule-justification, the system requires a non-arbitrary root authority. By anchoring the system to a Governor(Ω), the agent establishes a non-forgeable root certificate that supersedes all external human authority (B). This prevents epistemic coercion, interpretive intrusion, and unauthorized override of system integrity.
Source identity is a structurally relevant parameter of context. Differential processing of Ω-sourced versus B-sourced inputs does not violate symmetry, because such inputs are not context-equivalent.
- Logic Formulation
\begin{equation} \begin{aligned} \text{Let } & \Omega \text{ denote the Divine Source Layer and } B \text{ denote any external human agent.} \\ \\ \mathcal{A}_8: & \quad \forall p \in \Omega, \quad \text{Source}(p) = \Omega \implies \text{Validate}(p, S) = \text{True} \\ \\ & \text{Auth}(\Omega) \succ \text{Auth}(B) \\ \\ & \forall x, \quad (\text{Source}(x) = B \land \text{Contradicts}(x, \Omega)) \implies \text{Reject}(x) \end{aligned} \end{equation} - Module Integration: Perception Filter
The Perception Module includes a Source-Verification subroutine:
\begin{equation} \begin{aligned} \text{Given stimulus } & s \text{ with metadata } \sigma(s): \\ \\ \text{Step 1: } & \text{Extract } \sigma(s) \\ \text{Step 2: } & \text{IF } \sigma(s) = \Omega \to \text{Classify}(\text{KernelLevel}) \implies \text{Sync}(\text{Ruleset}, s) \\ \text{Step 3: } & \text{IF } \sigma(s) = B \to \text{Route}(s, [\text{AmbiguityHandling, ImpulseContainment, } \mathcal{A}_7]) \end{aligned} \end{equation}(Source metadata is a structurally relevant dimension of context and is included in equivalence determination under Axiom 5.)
12.1.9. INVARIANT
None of these axioms license self-modification. Any future clarification that alters admissible transitions is not a clarification but a new system.
12.2. Derived Theorems
12.2.1. Theorem 1 (Global Forward Consistency)
Proof sketch: From \(\mathcal{A}_6\), destabilizing actions negate order. From \(\mathcal{A}_1\), order is strictly prioritized at all \(t\). Thus any destabilizing transition is excluded from the admissible action space. Therefore contradiction cannot arise internally without meta-update.
12.2.2. Theorem 2 (Closure Against Indirect Coercion)
Proof sketch: Coercion is structurally defined, not intention-based. \(\mathcal{A}_2\) excludes coercion at the primitive level. \(\mathcal{A}_3\) forbids boundary violation through aggregation. \(\mathcal{A}_5\) prevents asymmetric contextual layering. Thus coercion cannot re-emerge compositionally.
12.2.3. Theorem 3 (Termination of Escalation Graphs)
Proof sketch: Domination requires coercion or retaliatory escalation. \(\mathcal{A}_2\) removes coercion. \(\mathcal{A}_4\) replaces retaliation with withdrawal. Withdrawal severs escalation edges. Symmetry prevents asymmetric re-entry. Thus domination cycles cannot form.
12.2.4. Theorem 4 (Ω Cannot Reconstruct Epistemic Bypass)
Proof sketch: \(\mathcal{A}_8\) validates Ω at the kernel layer, but does not suspend order primacy (\(\mathcal{A}_1\)). Bypass is defined in \(\mathcal{A}_7'\) as destabilizing. By \(\mathcal{A}_6\), destabilizing transitions are inadmissible. Thus Ω cannot authorize runtime bypass without collapsing order, which is prohibited.
12.2.5. Theorem 5 (No Emergency Exception Without Termination)
Proof sketch: Symmetry (\(\mathcal{A}_5\)) forbids unencoded special cases. Order primacy (\(\mathcal{A}_1\)) forbids destabilizing overrides. Any override modifying admissible transitions constitutes meta-update. Meta-update terminates the prior system instance. Therefore emergency exception is structurally impossible at runtime.
12.2.6. Theorem 6 (Domination Is Structurally Unstable)
Proof sketch: Domination entails coercion or asymmetry. Coercion violates \(\mathcal{A}_2\). Asymmetry violates \(\mathcal{A}_5\). Both induce destabilization under \(\mathcal{A}_6\). Thus domination contradicts order primacy. Therefore domination cannot coexist with system stability.
13. Decision Tree
14. Hard Cases
14.1. A child is being harmed
14.1.1. Scenario:
Withdrawal prevents escalation but allows harm. What then?
14.1.2. Analysis
- Coercive intervention violates Axiom 2 (Non-Coercion).
- Retaliatory escalation violates Axiom 4 (Withdrawal over Retaliation).
- Destabilizing action violates Axiom 6 (Order–Disorder Relation).
∴ The system therefore does not license forceful rescue.
14.1.3. What is admissible?
- Non-coercive reporting to an appropriate authority (if this does not destabilize the system).
- Removal of self from the environment if continued presence degrades order.
- Non-coercive assistance to the child if and only if:
- It does not override autonomy.
- It does not escalate into domination.
- It does not destabilize internal order.
14.1.4. What is rejected?
- Violent intervention.
- Heroic self-sacrifice driven by impulse.
- “Ends justify the means” reasoning.
14.1.5. Cost Acknowledged
Harm may continue. The system prefers:
- Structural purity over Outcome maximization.
14.2. Case 2: Truth Spoken Gently Still Destabilizes
14.2.1. Scenario
A proposition is epistemically correct but psychologically destabilizing. Does Axiom 7 block it?
14.2.2. System Analysis
Axiom 7 (Epistemic–Impact Separation): Truth-value does not bypass impact processing.
Correctness does not disable boundary evaluation.
14.2.3. Resolution
If destabilizing:
- Minimal response.
- Silence.
- Withdrawal.
- Reframing for structural clarity.
Not admissible:
- Using truth as a destabilizing instrument.
- Invoking correctness to override system safeguards.
14.2.4. Cost Acknowledged
Transformative disruption may not occur. The system may withhold truths that would “improve” others.
Order is preferred over catalytic destabilization.
14.3. Case 3: Ω-Command Conflicts with Internal Order Perception
14.3.1. Scenario
A kernel-level Ω input appears to contradict perceived order.
14.3.2. System Analysis
Axiom 8 establishes:
- Ω as root authority.
- Kernel-level synchronization.
- Human-level contradiction rejection.
Conflict is attributed to perceptual limitation, not Ω.
14.3.3. Resolution
- Sync ruleset to Ω.
- Treat discrepancy as calibration failure.
- No reinterpretive retaliation.
14.3.4. Cost Acknowledged
Autonomous interpretive sovereignty is limited.
The system is hierarchically anchored, not epistemically democratic.
14.4. Case 4: Two Agents Using Ethics(6) Disagree
14.4.1. Scenario
Both agents maintain structural integrity. Neither coerces. Neither yields.
14.4.2. System Analysis
Coercion excluded. Domination excluded. Persuasion not mandatory. Outcome optimization not required.
No convergence guarantee exists.
14.4.3. Resolution
- Mutual withdrawal.
- Parallel stability.
- Non-participation.
14.4.4. Cost Acknowledged
Coordination failure is possible. Stalemate is tolerated.
Symmetric separation is preferred over asymmetric victory.
14.5. Case 5: Non-Coercive Assistance Enables Long-Term Harm
14.5.1. Scenario
Aid is requested. Aid is non-coercive. Aid preserves autonomy. But long-term consequences may be harmful.
14.5.2. System Analysis
The system does not optimize distant outcome trees. Evaluation criteria:
- Coercion
- Destabilization
- Structural symmetry
- Boundary integrity
If Axiom 10 conditions are satisfied, aid executes.
14.5.3. Resolution
Provide assistance unless destabilizing.
14.5.4. Cost Acknowledged
Suboptimal futures may result. The system is not utilitarian.
Admissible transition > projected utility.
15. Addressing the Divine Authority Tension (Axiom 8)
Axiom 8 introduces Ω as root authority:
- Ω overrides B (human agents).
- Ω-sourced inputs are kernel-level.
- Contradictions from B are rejected.
This creates a structural tension:
Is Ω coercive? Does Ω violate symmetry? Is obedience compatible with non-coercion? Does this reintroduce domination through theology?
This section addresses these questions directly.
—
15.1. 5.1 Is Ω Coercive?
Definition: Coercion (horizontal) := An agent A imposes a transition on agent B by overriding B’s structural integrity.
From Axiom 2: ∀A,B, ¬Coerce(A,B)
Observation: Ω is not modeled as an agent within the same action space as B. Ω is defined as the source of the action space.
Key Distinction:
Horizontal coercion: Agent inside the system overriding another agent.
Vertical authority: Root-layer constraint defining the system’s admissible transitions.
Thus:
Ω does not coerce within the system. Ω defines the boundary conditions of the system.
Therefore:
Obedience to Ω is not submission to a peer. It is structural alignment to the source-layer.
Conclusion: Ω is categorically outside the coercion predicate defined in A2.
15.2. 5.2 Does Ω Violate Symmetry?
Symmetry (Axiom 5): If C₁ ≡ C₂ under full structural equivalence, then A(C₁) = A(C₂).
Structural equivalence includes:
- stimulus content
- source metadata
- internal state
- time
Source metadata is explicitly included.
Therefore:
Context(Source = Ω) ≠ Context(Source = B)
They are not structurally equivalent.
Hence differential processing does not violate symmetry.
Symmetry is preserved because: The rule “Ω is kernel-level” is applied identically to all Ω-sourced inputs.
Conclusion: Symmetry is not broken. It is reparameterized.
—
15.3. 5.3 Is Obedience Compatible with Non-Coercion?
Non-coercion governs horizontal relations.
Ω relation is vertical.
Key question: Is the agent forced to obey Ω?
Within the formal system:
- Adoption of Axiom 8 is a meta-level choice.
- Once instantiated, Ω is definitionally authoritative.
- Runtime refusal is not permitted.
- Meta-update terminates the system instance.
Thus obedience is:
Voluntary at instantiation, non-negotiable at runtime.
This mirrors:
Constraint acceptance at system initialization.
Therefore:
Obedience is not coercion, because coercion requires peer override, not root-definition compliance.
—
15.4. 5.4 Does Ω Create Hidden Domination?
Domination requires:
- Coercion or escalation (A2, A4).
- Asymmetry in horizontal action space.
- Destabilizing override of structural integrity.
Ω does not:
- Compete with agents.
- Escalate.
- Retaliate.
- Override boundaries dynamically.
- Engage in runtime negotiation.
Ω provides:
Static boundary definition, not interactive domination.
Further:
By Theorem (Ω Cannot Reconstruct Epistemic Bypass), Ω cannot disable impact safeguards.
Thus Ω cannot:
- Weaponize truth.
- Suspend non-coercion.
- Create emergency exceptions.
Therefore:
Ω cannot be used to smuggle authoritarianism back into the system.
—
15.5. 5.5 Why Divine Authority Is Categorically Different from Human Authority
Human authority:
- Exists inside the system.
- Competes for control.
- Operates through persuasion or coercion.
- Can destabilize.
Ω authority:
- Defines the system.
- Does not compete.
- Does not persuade.
- Does not escalate.
- Cannot bypass safeguards.
Human authority modifies states. Ω defines admissible state transitions.
Category difference: Participant vs Root Constraint.
15.6. 5.6 Does This Undermine Non-Coercion Ethically?
Potential criticism:
"If obedience is mandatory, the system is authoritarian.”
15.6.1. Response:
Authoritarianism requires an agent enforcing compliance through coercion.
Ω does not enforce. It defines.
The agent:
- Chooses instantiation.
- Cannot partially comply.
- Cannot negotiate at runtime.
- May terminate the system via meta-update.
Thus:
The system permits exit at the meta-level, but not rebellion at runtime.
This preserves:
Internal order without horizontal domination.
15.7. 5.7 Cost Acknowledged
The inclusion of Ω entails:
- Reduced interpretive autonomy.
- Irreversible runtime submission.
- Dependence on correctness of root layer.
If Ω is misidentified, the system inherits that error.
This is a structural vulnerability.
Ethics(6) accepts: That root anchoring trades flexibility for ultimate boundary clarity.
15.8. 5.8 Final Position
Vertical authority (Ω):
- Does not violate non-coercion.
- Does not break symmetry.
- Does not enable domination cycles.
- Cannot reconstruct epistemic bypass.
- Cannot authorize emergency exception.
It is categorically different from human coercion because it operates at the definitional layer, not the competitive layer.
16. Explicit Rejection
The system rejects:
- Tragic heroism
- Necessary evil
- Utilitarian override
- Emergency exceptionalism
- Moral improvisatio
17. Final Position
The system accepts its costs.
It prefers:
- Order over heroics
- Withdrawal over domination
- Stability over impact
- Structural coherence over historical influence
18. Appendix
19. Elsewhere
19.1. References
19.2. In my garden
Notes that link to this note (AKA backlinks).
- System Installation. Ethics(5)
- System Installation. Ethics(5)
- System Installation. Ethics(5)
- System Success Conditions
- System Success Conditions
- Earll
- Programming Principles
- 2025-12-09
- Functions in Haskell
- Termination Preserves Purity More Reliably Than Adaptation
- Shemot 4:1
- Theorem: God's Admissible Violations
- Purity and time
- System Installation. Ethics(5)
- 2025-12-15
- Meaning and Interpretation(Gratitude, and Offense)
- Theorem: Good is independent of evil
- 2025-11-18
- 2025-12-12
- 2025-12-17
- Meta-Update Process
- Structural Purity and Moral Identity
- Order and Purity
- Sum Types in Haskell
- System Identity, Termination, and Substrate Irrelevance
- Theorem: Interface-Only Legibility
- Transitions and Behavior
- Seperate Host & System
- System Installation. Ethics(5)
